Applications
Applications represent one or more integrations with your brand’s portals, applications, and resources. In Strivacity, an Application is a set of policies and configurations applied to one or more of a brand’s portals. Applications integrate with your brand’s portals via configurations contained in Application Clients. Application Clients share the same policies and allow multiple brand portals to be governed by the same set of policies.
Integration approaches
Strivacity supports multiple approaches for integrating authentication and customer identity management into your applications.
The recommended approach is using OIDC-based redirection flows, where authentication is performed by Strivacity-hosted experiences. Strivacity also supports embedded and API-driven authentication experiences, as well as SAML2 integrations for enterprise and legacy applications.
For more information, see:
Application types
You can choose between three types of applications, depending on your CIAM needs:
Simple applications
A simple application is designed for a single, unified user base, where all users share the same authentication experience and access patterns.
You can choose this type of application if you don’t have complex organizational needs.
This diagram illustrates the relationship between the identity store, the application, its multiple clients, assigned policies, and your brand portals:
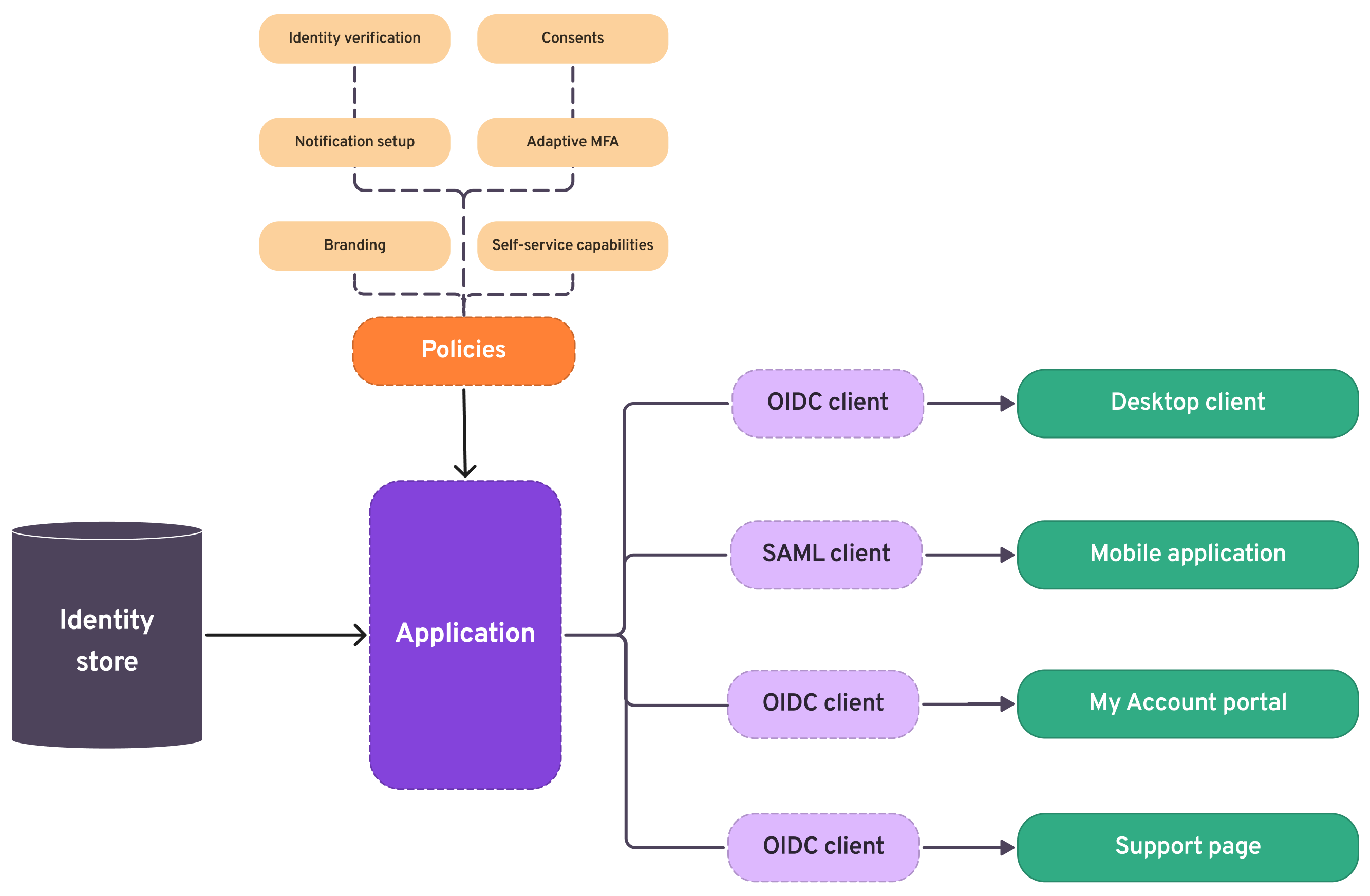
Simple applications
Organization-enabled applications
An organization-enabled application supports multiple distinct user groups (organizations), allowing each to independently manage its own users and access while sharing the same underlying application and identity infrastructure.
This application type can provide sign-in journeys for different groups of business customers. Best for complex B2B use cases (such as white labeling in a B2B setting) where no personal accounts are needed.
This diagram illustrates the relationship between the identity store, organizations, policies, the application, its multiple clients, and your brand portals:
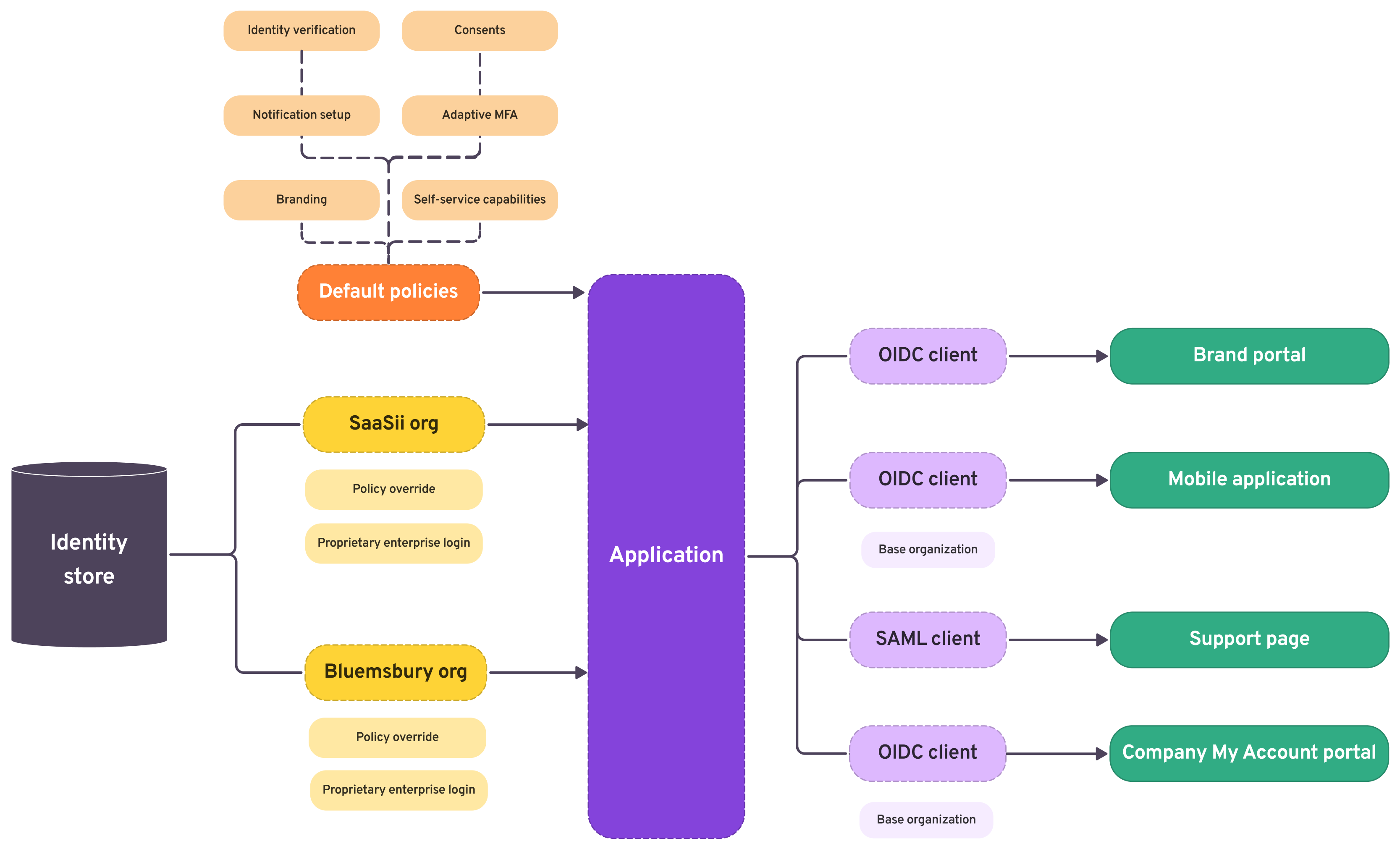
Organization-only applications
Hybrid applications
A hybrid application supports both individual users and multiple organizations, enabling shared experiences alongside organization-specific user management and delegated administration within the same application.
This applicaiton type can accomodate both B2B and B2C customers. You can provide sign-in for enterprise identities and non-organizational users without any hassle.
This diagram illustrates the relationship between the identity store, organizations, policies, the application, its multiple clients, and your brand portals:
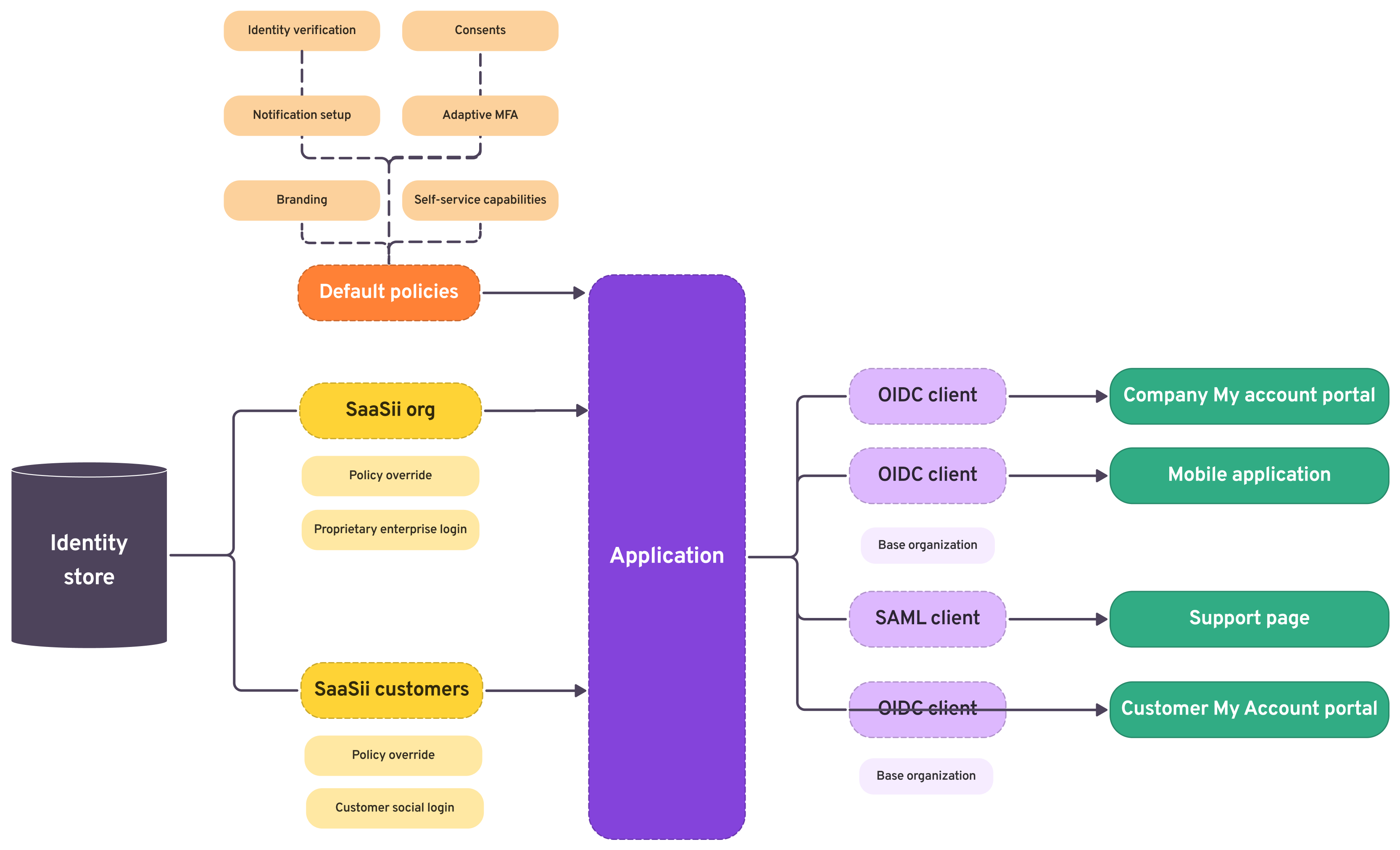
Hybrid applications
Base organizationsClients can have base organizations configured. Base organizations close off a specific chunk of the organizational hierarchy and restrict the client to the organizations in that extracted hierarchy.
Filtering applications
After selecting Applications from the left-hand menu on the admin dashboard, you can filter the applications list by Name, OIDC client ID, and Policy tags to quickly locate specific applications.
This filtering feature helps administrators quickly locate specific applications among a large set, making it easier to manage and configure applications based on key attributes.
When you apply filters, the URL automatically updates to reflect your filter selection. This allows you to share or bookmark your current view. Your last-used filters are remembered: if you navigate away and return, the same filters will be applied.
Updated 24 days ago
