Identity verification
Overview
Identity verification is an add-on capability. Check with your Strivacity sales or customer success representative to add these features to your service.
Establishing trust in your customers' identities prevents the misuse of your services, protects your brand’s reputation, and may be necessary to comply with regulations.
Strivacity's identity verification features strengthen the security of your applications by confirming the identity of your customers online without getting in the way of usability. It offers a secure way to make sure the people interacting with your brand are legitimate customers while preserving customer satisfaction.
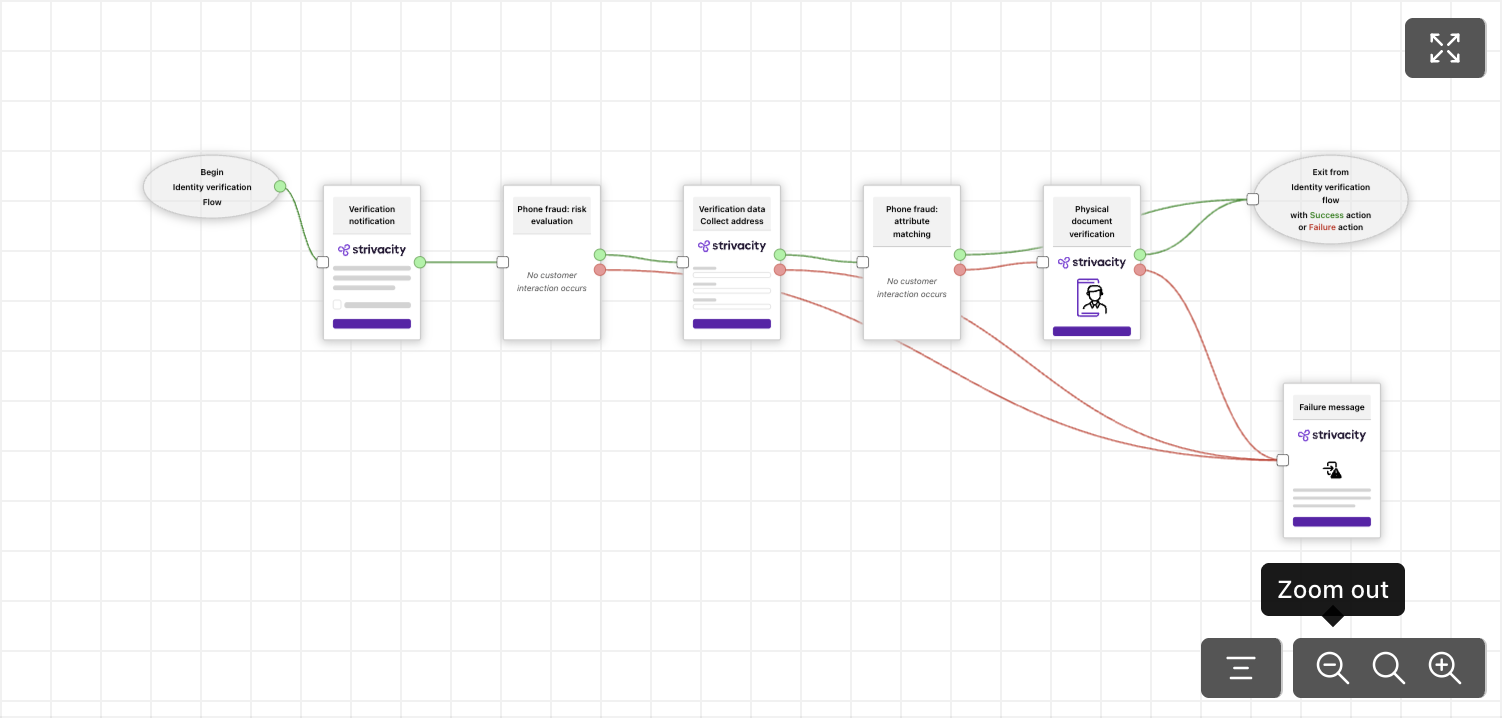
A preview of the identity verification workflow
Identity verification modules
Identity verification policies consist of several modules and steps that you can assemble according to your risk tolerance. You can find out more about each module at the links:
- Custom messaging
- Data collection
- Data requests from external services (via event hooks)
- Data dispatch to external services (via event hooks)
- Risk evaluation
- Policy workflow preview
Updated 17 days ago
