Lifecycle event hooks
Learn how to setup and use Lifecycle Event Hooks to integrate your customer facing applications with any other homegrown systems or third-party products that you may own, such as CRM or Marketing Hubs
Overview
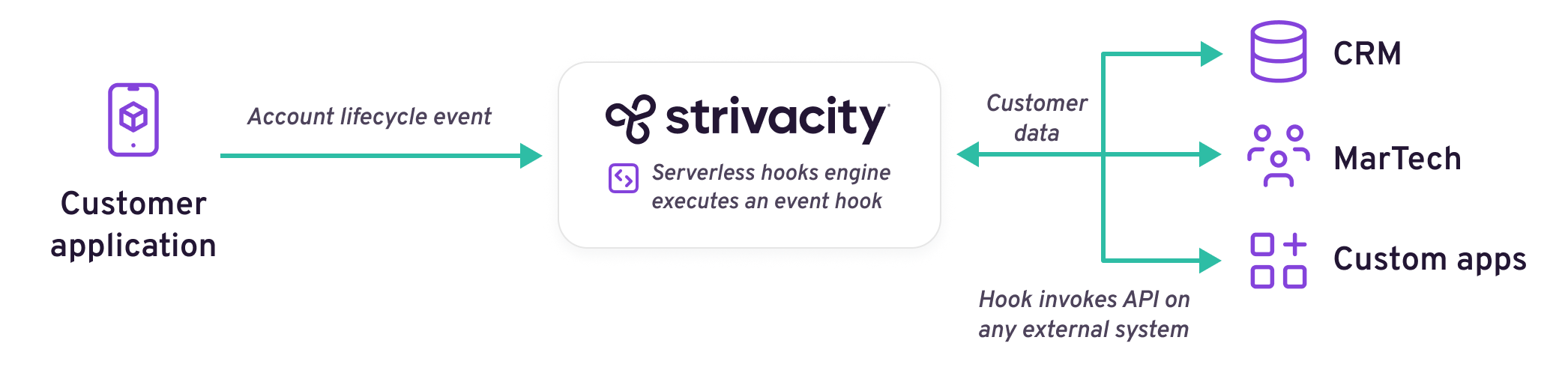
The Strivacity Lifecycle Event Hooks (LEH) provide a method to integrate your customer facing applications with homegrown systems and third-party products.
Lifecycle Event Hooks can be used in many different ways. Some of the more common use cases involve customizing registration, updating or fetching data from remote systems such as CRMs during certain lifecycle events, or alerting third-party systems on specific events of interest such as:
- Deep customization of registration - Brands often require extensive customization of the registration process. Information from external systems, such as CRMs, may be required to keep multiple disparate databases in sync. Often a brand will pull this in during a pre-registration hook to allow it to be submitted during the Registration process. New or additional information can be easily synchronized back to an external system in real time.
- Customer data synchronization - Brands may require keeping disparate customer databases in sync, such as the customer identity store and a remote CRM system. Customer Lifecycle Event Hooks can be used to dispatch information about events of interest to these remote systems.
- Alerting - Brands may desire to be alerted when an event of interest occurs, such as a password reset request.
- Consume and use threat information - Insert threat detection and mitigation into any point in the customer lifecycle, giving security teams highly contextual alerting when threats are detected. Existing threat information can be used to make risk analysis decisions.
An actual Lifecycle Event Hook is a brand-provided snippet of javascript code that executes at predefined points in a customer's lifecycle, such as registration, login, consent opt in or out, or account deletion. A full listing of events and how they can be used is provided below. All snippet code executes within the context of the Strivacity platform in a safe and secure sandboxed environment. Two modes are supported:
- Synchronous - Control is transferred to the script for execution. Upon completion, control is returned to Strivacity's normal workflow execution.
- Asynchronous - The script is executed but control is not transferred, and Strivacity continues on with its normal workflow execution.
The brand decides and can configure, in the administration console, whether an event hook should execute synchronously or asynchronously.
Plugin library
Plugins make publishing lifecycle event hooks easy.
The plugin library provides you with hook templates for common use cases. Event hook templates are off-the-shelf integration and advanced capability packages that you can customize for your own needs and add to your applications.
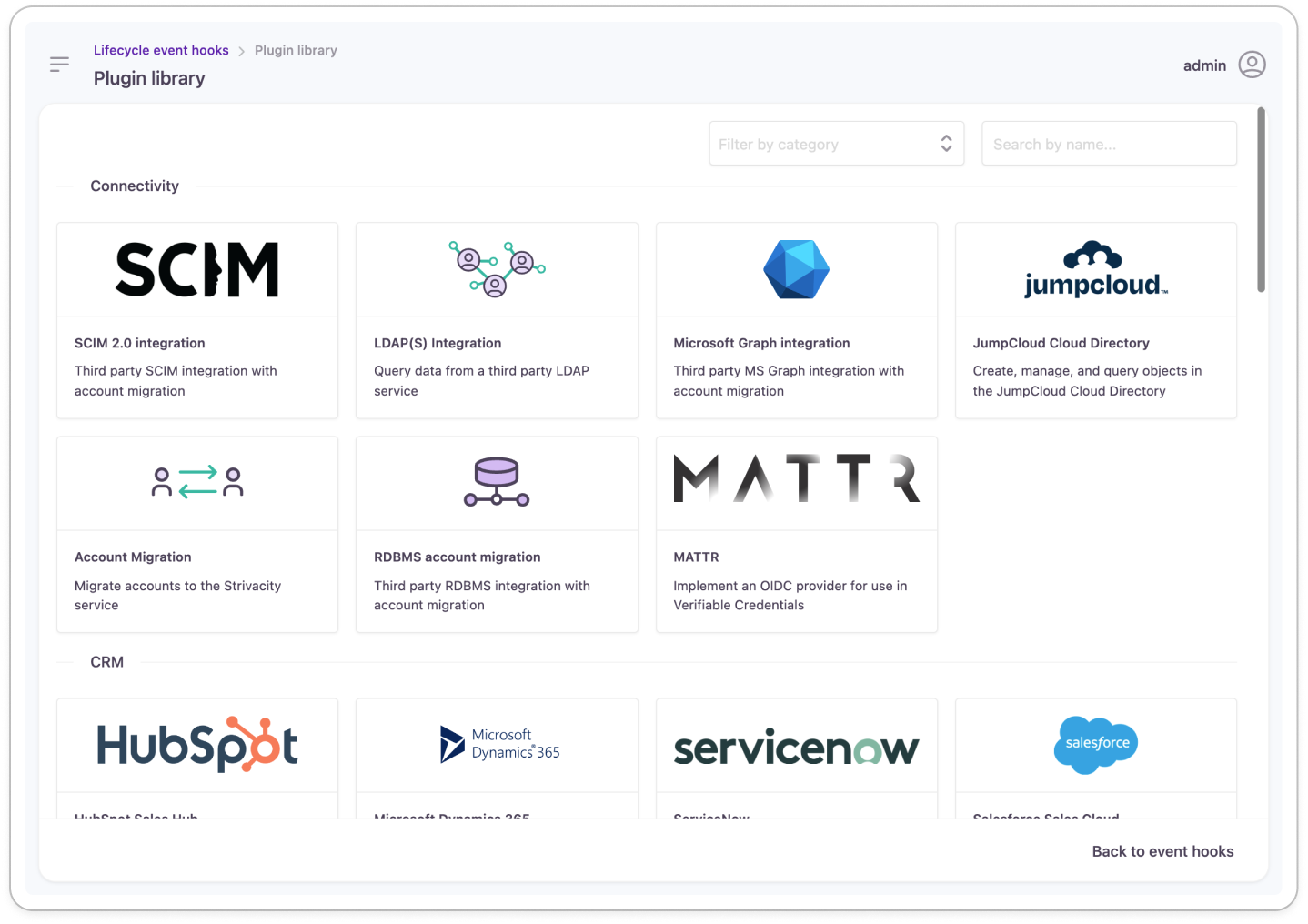
Plugin library preview
The template packages come with all the necessary dependencies set up. Their point-of-entry into the customer lifecycle is also configured, so you don’t have to think about selecting the right event hook type:
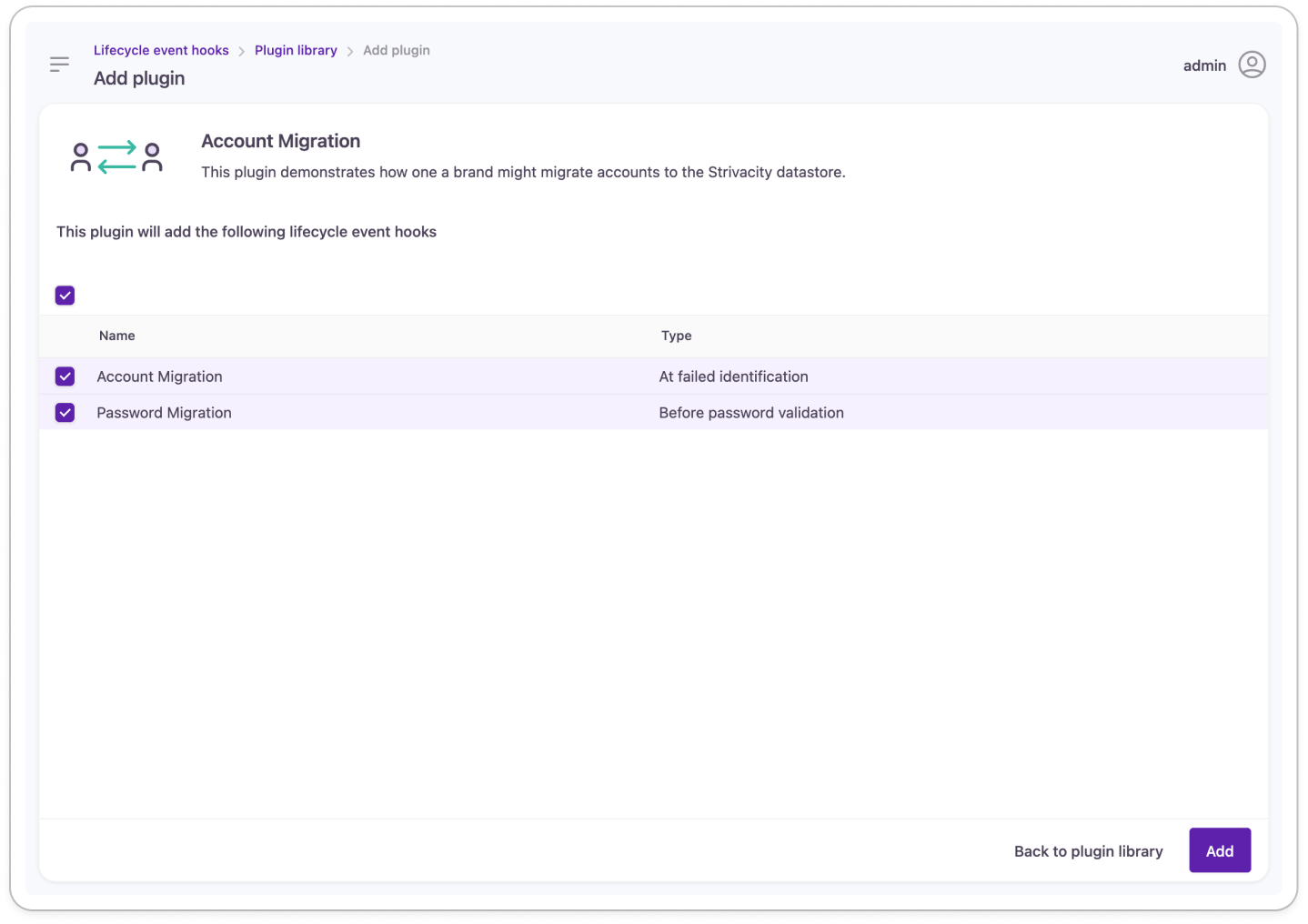
Lifecycle event hook templates for account migration
After selecting the capability that you want to add to your application, you can publish the template as a new lifecycle event hook. You can customize the code inside the hook and assign it to an application to have it deployed.
Supported events
Multi-stage progressive profiling
Strivacity’s "Before registration" and "Before progressive profiling" event hooks allow you to introduce progressive profiling steps to customer journeys on your conditions. You can configure steps to adapt to your customers' activity to make data collection a more personalized experience.
The following table shows a summary of the events that are supported by Strivacity with examples of how they can be used:
At failed...
| Event type | Purpose |
|---|---|
| Authentication | This event occurs when customer authentication or registration fails for some reason. Use this event in the workflow to hook in your custom error message or to redirect your customer in case they're denied authentication. |
| Identification | This event is triggered when a customer identity coming from an external identity provider doesn't exist in the application's identity store.
|
After...
| Event type | Purpose |
|---|---|
| Self-service login | Triggers an external event or fetches data from an external system after the customer has successfully authenticated and they have an ID token. |
| Consent update | This event is triggered after a customer opts into or opts our of any consents at registration or self-service. Use this event to synchronize consents with other third-party systems such as marketing hubs, email advertising platforms or CRMs. |
| Identity verification | This event launches after the identity verification workflow has finished. |
| Customer identification | This event is triggered once the customer has provided their identifier (email address or username) and before they are asked for any factor of authentication. This can be used to step-up or step-down the authentication journey based on an external event, risk data from an external system, or other account attribute information for that customer. |
| MFA change | Triggers an external event or fetches data from an external system once the customer has completed the verification of a new/additional MFA factor during enrollment or removed a factor. |
| Registration | Once a customer has successfully completed the account registration process this event is triggered to trigger an external event or fetch/update data with an external system. |
| External login | Triggers an external event or fetches data from an external system once a customer has successfully completed registration using a social login provider. |
| Password change | This event is triggered after a new password has been created. The event hook can be used to sync passwords to an external identity store and is applied to an identity store rather than an application. |
Before...
| Event type | Purpose |
|---|---|
| Password validation | This event is triggered when a customer identity is found eligible to be migrated from an external identity store. |
| Identity verification | This event launches before the identity verification workflow starts. |
| ID token generation | Used to add additional claims to OIDC and OAUTH by fetching data from an external systems before the ID token is generated. |
| SAML2 assertion generation | This event triggers before assertion is generated during SAML login flow. You can add additional assertion data to the SAML assertion or deny the request based on certain criteria. |
| Progressive profiling | This event launches after a customer completes the first step of registration. You can add extra steps to the registration workflow for various progressive profiling scenarios:
|
| Registration | Fetches data from an external system so it can be used and stored with a customer's account during the account registration process. |
| Multi stage registration | Allows you to break down the registration form into smaller chunks and present the parts in a multi-step manner. In the hook, you can include attributes that are displayed at registration, consents assigned to the application in use, and the identifier(s) supported by the identity store. A summary screen at the end of the registration flow will automatically display any attributes, consents, and identifiers that weren't used in this hook but are part of the flow. The hook can be configured to skip the summary screen if only optional fields or consents remain at the end. |
| External registration | Allows control over what happens after a new account is authenticated through an external provider. It allows you to suppress and silently accept confirmation screens, and it also provides a way to link to other, already existing accounts, other than what the default linking target would be. |
| Authenticator enrollment | This event hook allows you to customize the MFA enrollment workflow based on user behavior or information collected from external systems such as CRMs, marketing hubs, or data analytics platforms. You can control the appearance of enabled authenticators such as email, phone, platform biometrics, etc. Methods associated with those authenticators, such as magic links or passcodes cannot be controlled from the event hook. You can enforce the use of a specific email address or phone number authenticator from the hook, even if restrictions to existing email addresses or phone numbers apply. You can also force users to enroll one of the enabled authenticators if every method is set to optional in the basic MFA flow. |
How It Works
Example Usage Scenarios
- Customize registration by bringing in and persisting external data
- Establish a single source of truth and synchronize customer data across multiple systems
- Insert threat detection and response into any point in the customer lifecycle
- Alert your customer service or security teams to events of interest
- Trigger workflow in external orchestration systems when customers perform specific actions
- Make location based decisions in customer login and registration flows
Updated 10 days ago
